Difference between revisions of "Mass surveillance"
m (Operating System added) |
m (re arrange) |
||
| Line 48: | Line 48: | ||
While the [[Internet]] was designed to be decentralised, and so non-trivial to censor/monitor, the [[NSA]] has been consistently trying for decades to stifle an effective roll out of [[cryptography]] for decades. Several [[whistleblower]]s have revealed that the [[NSA]] has fiber optic splitters which allow for monitoring of huge amounts of data. The connection with internet [[censorship]] is clear; when everyone's posting is watched, unwanted content is easily removed, moreover, [[self-censorship]] may become endemic due to fear of reprisals - [[Webster Tarpley]] and others have suggested that this perspective may help understand the [[Edward Snowden Affair]], and would tally with a large number of disclosures of mass surveillance of other natures made recently. | While the [[Internet]] was designed to be decentralised, and so non-trivial to censor/monitor, the [[NSA]] has been consistently trying for decades to stifle an effective roll out of [[cryptography]] for decades. Several [[whistleblower]]s have revealed that the [[NSA]] has fiber optic splitters which allow for monitoring of huge amounts of data. The connection with internet [[censorship]] is clear; when everyone's posting is watched, unwanted content is easily removed, moreover, [[self-censorship]] may become endemic due to fear of reprisals - [[Webster Tarpley]] and others have suggested that this perspective may help understand the [[Edward Snowden Affair]], and would tally with a large number of disclosures of mass surveillance of other natures made recently. | ||
| − | ==Operating System== | + | ====Operating System==== |
Common [[operating systems]] on the market like [[Microsoft]]s [[Windows]], [[Apple]]s [[IOS]] and [[Google]]s [[Android]] are mostly used with an online connection. The devices that run these operating systems, by design will become the first functioning part of the data collection process over the Internet which the user has no real overview of. | Common [[operating systems]] on the market like [[Microsoft]]s [[Windows]], [[Apple]]s [[IOS]] and [[Google]]s [[Android]] are mostly used with an online connection. The devices that run these operating systems, by design will become the first functioning part of the data collection process over the Internet which the user has no real overview of. | ||
Revision as of 18:15, 22 November 2019
 | |
| Interest of | • AMD • Apple • Jacob Applebaum • Below Gotham Labs • Big Brother Watch • Carole Cadwalladr • Dark Politricks • Michael Drury • ID2020 • International Festival of Whistleblowing Dissent and Accountability • Philip Matthews • Microsoft • William Odom • Privacy International • Security Without Borders • The Juice Media • The Paypal Mafia |
| Subpage(s) | •Mass surveillance/Technology |
| Wholesale surveillance of the citizenry is the new normal, introduced under the smokescreen of the "war on terror". In the "art of warfare" surveillance is taught as a preparatory act for more invasive measures such as the suspension of habeas corpus (i.e. the Patriot Act) or other covert operations. | |
Mass surveillance is increasingly carried out by governments the world over. The most common purported justification is the "war on terror". The extent is not publicly disclosed, but rapid development in mass surveillance technologies and large budgets which remain classified behind veils of "national security" suggest that its extent and sophistication may be more than is generally realised.
Contents
Official narrative
Mass surveillance is usually presented by the commercially-controlled media as being a necessary evil to fight the "war on terror". The official opposition narrative - the other end of the spectrum of opinion presented by corporate media - does not question that civil rights must be trade off for protection against "terrorism", so if differs only about only how much mass surveillance is an acceptable compromise between safety and liberty. Both the official narrative and its opposition neglect to mention that, since Edward Snowden's revelations have demonstrated that illegal mass surveillance was being carried out widely and systematically, and since no one has been charged - or even accused - as a result, it is reasonable to assume that the major limitations to mass surveillance are technical rather than legal.
Problems
No evidence has been presented that mass surveillance was intended to stopping "terrorism". Several NSA whistleblowers such as William Binney, Russell Tice and Thomas Drake have directly challenged this claim, arguing that by contrast, it makes the US public less safe rather than more.[1] The "Surveillance State Repeal Act" was introduced into US Congress in March 2015, to end the US PATRIOT Act and reform the NSA.
"Corrupt power grab?"
A simpler explanation suggests that it is "a corrupt power grab... not an effort aimed at stopping terrorism".[2] In 2017, the United Nations' Special Rapporteur on the right to privacy echoed this sentiment in more diplomat terms. Criticising recent mass surveillance laws in France, Germany, the UK and the USA, he stated that they are "predicated on the... disproportionate though understandable fear that electorates may have in the face of the threat of terrorism" but are informed by "little or no evidence" of their "efficacy or... proportionality".[3]
| Bill Binney on mass surveillance |
"War on Terror"
- Full article:
 “War on Terror”
“War on Terror”
- Full article:
The "War on Terror" has repeatedly used false flag terror attacks, in conjunction with a compliant commercially-controlled media to try to instill fear in people. Deliberate vagueness about laws and increasing use of guilt by association are intended to chill dissent in an effort to introduce new mass surveillance technologies. This has been particularly useful in countries such as the USA and the UK which had laws and traditions about privacy which, if enforced, would have prevented such surveillance. A widespread culture of impunity for those who control the structures of Western nation states mean that few (if any?) serious commentators regard such objections to mass surveillance as effective in practice - the only remaining limitations on data collection are purely technical in nature. UN Special Rapporteur on Privacy, Joseph Cannataci referred UK's oversight of surveillance as “worse than a bad joke.”[4]
Origins
Harry S. Truman was concerned about the power accrued by both the CIA and the FBI. In 1947 he wrote about the FBI: "Edgar Hoover's orgnization would make a good start toward a citizen spy system. Not for me."[5]
Modern Methods
The rise of electronic communication methods have lead to a burgeoning of the mass surveillance in the 21st century. The blatant - and unpunished - disregard for the law by both NSA and GCHQ should leave little doubt that legal restrictions are mostly left for show.
Audio Surveillance
Various electronic devices have made audio recordings and for internet behavior.[6][7]
XBoxes
In August 2019, Motherboard wrote that Microsoft contractors have admitted to listening to users of XBoxes they "said that recordings were sometimes triggered and recorded by mistake".[8]
Televisions
- Full article: Television
- Full article: Television
"Fake off mode".
Internet Surveillance
- Full article: Internet/Surveillance
- Full article: Internet/Surveillance
While the Internet was designed to be decentralised, and so non-trivial to censor/monitor, the NSA has been consistently trying for decades to stifle an effective roll out of cryptography for decades. Several whistleblowers have revealed that the NSA has fiber optic splitters which allow for monitoring of huge amounts of data. The connection with internet censorship is clear; when everyone's posting is watched, unwanted content is easily removed, moreover, self-censorship may become endemic due to fear of reprisals - Webster Tarpley and others have suggested that this perspective may help understand the Edward Snowden Affair, and would tally with a large number of disclosures of mass surveillance of other natures made recently.
Operating System
Common operating systems on the market like Microsofts Windows, Apples IOS and Googles Android are mostly used with an online connection. The devices that run these operating systems, by design will become the first functioning part of the data collection process over the Internet which the user has no real overview of.
Watch lists
- Full article: Watch lists
- Full article: Watch lists
The official narrative of watch lists is that they help assist law enforcement in prevention of terrorist activity. In practice, however, they are better understood as a means of mass surveillance (because everyone has to give their details, to prove that they are not on a watch list). Since the management of these lists is completely opaque, they can also be understood as a precursor to the enforcement of a heavy-handed police state - one in which individual rights are conditional and can be revoked at a moment's notice without the need for such matters as evidence of wrong doing.
Postal surveillance
- Full article: Mail Isolation Control and Tracking
- Full article: Mail Isolation Control and Tracking
After the 2001 anthrax attacks, which were initially blamed on "Islamic terrorists", although the anthrax was later proved to have come from a US military laboratory, the US government secretly instituted a program to photograph all the mail sent in the US. This went undisclosed to the general public for over a decade. In 2015, it was revealed that the US Postal Inspection Service had installed a utility box "positioned to capture and record the license plates and facial features of customers leaving a Golden Post Office." [9]
Cellphone location data
In 2013, in response to a subpoena for cellphone data, the NSA claimed that "The government does not possess the records the defendant seeks", i.e. specifically denied that they had collected cellphone data, although the Foreign Intelligence Surveillance Act court order stated that they could have collected this data.[10] At the same time all of this type surveillance data is available for the cellphone network providers, whose data the NSA may access with ease, irregardless of any legal regulation. Apple does have a history of collecting location data secretly.[11]
Emerging surveillance Technologies
- Full article: Mass surveillance/Technology
- Full article: Mass surveillance/Technology
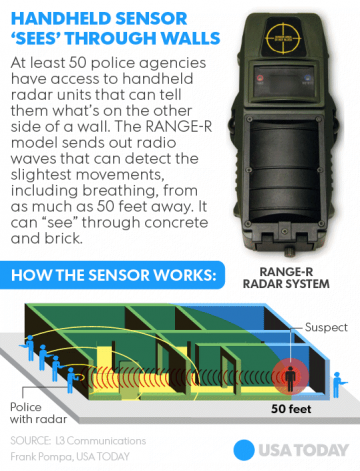
The US military has developed new surveillance technologies which - with or without trialling in war zones overseas - are being rolled out across the country. Legal barriers are no effective impediment in what many have termed a police state. These include surveillance by Reaper Drones[12], Hand Held Radar[13], Cellphone Surveillance Tools[14], X-Ray vans[15] and automatic recognitino of faces, car license plates and other data from CCTV by computers.[16][17]
Response
The commercially-controlled media has not dwelt on the illegality of mass surveillance carried out continuously by intelligence agencies. Instead, the political establishment has moved to legalise such actions, under the pretext of the threat of "terrorism". Only token discussion has ever been made in corporate meia about whether mass surveillance is helpful in this regard.
“Perhaps the most curious thing about the response to revelations concerning the extent of modern mass surveillance is that most people in the West have not seemed to mind; we have not perceptibly altered our online behavior or demanded a response from our governments. We seem not able or willing to grasp the implications, and we have shown a weary cynicism that evidently masks a deeper indifference. Many have shown an eager complicity, free of defensiveness. If you are innocent, you have nothing to fear, we insist, forgetting the innocence of millions interned and murdered by Western governments within living memory. Surveillance will keep us safe from our enemies, we say, obediently accepting the pronouncements of our governments on the identities of our enemies and the proper sources of our terror.”
Amanda Power (February 2016) Under Watchful Eyes [18]
Examples
| Page name | Date | Description |
|---|---|---|
| "Digital identity" | information used by computer systems to represent a person or group. | |
| "Smart city" | A prison-city with an algorithm as warden | |
| "Strike Hard Campaign" | A research project into repressive social control carried out against Chinese Muslims. | |
| 1-3-30 Plan | A Rockefeller Foundation sponsored large scale surveillance proposal and simulation. Held April 2020 | |
| Australia/Universal surveillance | ||
| CONTEST | ||
| ECHELON | ||
| The world's most popular social network, with over 1,000,000,000 users in 2014. | ||
| Global Internet/Skynet conglomerate | ||
| InfraGard | Program to turn private-sector corporations - having access to enormous amounts of information on citizens - into surrogate eyes and ears for the FBI. | |
| Inslaw | Complex financial/political fraud the full dimensions of which were never uncovered, but some of which were forced onto the official record. | |
| Internet/Surveillance | Wholesale surveillance of the citizenry is the new normal, introduced under the smokescreen of the "war on terror". | |
| LifeLog | A DARPA project to create a system of collecting data about users in a single place. It was cancelled when Facebook started, in February 2004. | |
| Mail Isolation Control and Tracking | A US mail program to photograph of the exterior of every piece of mail that is processed in the United States. | |
| Maximator-Alliance | Intelligence Alliance, similar to Five Eyes. | |
| NSA/Boundless Informant | ||
| NSA/PRISM | ||
| NewsGuard | A tech company which is teaming up with Microsoft as regards "fake news" | |
| Project SHAMROCK | NSA surveillance program | |
| Romas/COIN | US SIGINT program of mass surveillance and data mining operated against the Arab world through 2009-2011 | |
| Satellite | ||
| Sentient World Simulation | ||
| ShadowNet | ||
| Surveillance and censorship program | The UK government's 'Surveillance and censorship' (SAC) program is alleged by Kevin Galalae to be a part of the their CONTEST 'war on terror' strategy. He describes it as a project to 'brainwash the young and the impressionable to hold skewed and hypocritical views in line with the British Government’s foreign and domestic policy objectives'. | |
| United States Postal Inspection Service | The "law enforcement arm of the United States Postal Service." |
A Mass surveillance victim on Wikispooks
| Title | Date | Description |
|---|---|---|
| Denis Rancourt | Formerly a former tenured professor of physics, Rancourt was dismissed after covert surveillance and legal maneuverings by the University of Ottawa in Canada. |
Related Quotations
| Page | Quote | Author | Date |
|---|---|---|---|
| "Vaccine passport" | “Eventually we will need some digital certificates to show who has recovered or been tested (for COVID-19) recently, or when we have a vaccine, who has received it.” | Bill Gates | 18 March 2020 |
| "Vaccine passport" | ““We have no plans to introduce them” said the prime minister (Boris Johnson) when talking about so-called vaccine passports. “I certainly am not planning to issue any vaccine passports and I don't know anyone else in government who would”, said Michael Gove and “no one has been given or will be required to have a vaccine passport” said the man himself, the vaccine's minister Nadhim Zahawi. Now in a slope slipperier than the ones Eddie the Eagle used to chuck himself off, it seems the government have changed their mind. First it was talk of nightclubs or sports events, and now the government is I quote “not ruling out making students be fully vaccinated to attend lectures”.... I guarantee you this is not where it ends.” | Michelle Dewberry | 26 July 2021 |
| Australia/1975 coup d'état | “There were a number of points of tension between Whitlam's government and the United States intelligence apparatus. Whitlam had close ties with the United States, in 1964 receiving a "Leader" travel grant from the U.S. Department of State to spend three months studying under U.S. government and military officials.
After coming to power, Whitlam quickly removed the last Australian troops from Vietnam. Whitlam government ministers criticised the US bombing of North Vietnam at the end of 1972. The US complained diplomatically about the criticism. In March 1973, US secretary of State William Rogers told Richard Nixon that "the leftists [within the Labor Party would] try to throw overboard all military alliances and eject our highly classified US defence space installations from Australia". In 1973, Whitlam ordered the Australian security organisation ASIS to close its operation in Chile, where it was working as a proxy for the CIA in opposition to Chile's president Salvador Allende. Whitlam's Attorney-General Lionel Murphy used the Australian Federal Police to conduct a raid on the headquarters of the Australian Security Intelligence Organisation (ASIO) in March 1973. CIA Chief of Counter-Intelligence, James Angleton, later said Murphy had "barged in and tried to destroy the delicate mechanism of internal security". Australian journalist Brian Toohey said that Angleton considered then Australian Prime Minister Gough Whitlam a "serious threat" to the US and was concerned after the 1973 raid on ASIO headquarters. In 1974, Angleton sought to instigate the removal of Whitlam from office by having CIA station chief in Canberra, John Walker, ask the director general of ASIO, Peter Barbour, to make a false declaration that Whitlam had lied about the raid in Parliament. Barbour refused to make the statement. In 1974, Whitlam ordered the head of ASIO, Peter Barbour, to sever all ties with the CIA. Barbour ignored Whitlam's order and contact between Australian and US security agencies was driven underground. Whitlam later established a royal commission into intelligence and security. Jim Cairns became Deputy Prime Minister after the 1974 election. He was viewed by US secretary of state Henry Kissinger and defence secretary James Schlesinger as "a radical with strong anti-American and pro-Chinese sympathies". The US administration was concerned that he would have access to classified United States intelligence. Whitlam instantly dismissed ASIS chief WT Robinson in 1975 after discovering ASIS had assisted the Timorese Democratic Union in an attempted coup against the Portuguese administration in Timor, without informing Whitlam's government. Whitlam threatened to reveal the identities of CIA agents working in Australia. He also threatened not to renew the lease of the US spy base at Pine Gap, which was due to expire on 10 December 1975. The US was also concerned about Whitlam's intentions towards its spy base at Nurrungar.” | Wikipedia | 2022 |
| Backdoor | “Every year, we learn about some issue in WhatsApp that puts everything on their users' devices at risk. Which means it's almost certain that a new security flaw already exists there. Such issues are hardly incidental – they are planted backdoors. If one backdoor is discovered and has to be removed, another one is added” | Pavel Durov | 5 October 2022 |
| CONTEST/Prevent | “I hear criticism but I absolutely don't accept it. Prevent is not about spying on communities. It's about safeguarding.” | 2017 | |
| China | “The US believes a suspected Chinese surveillance balloon that was shot down over its territory is part of a wider fleet that has spanned five continents.
"The United States was not the only target of this broader programme," Secretary of State Antony Blinken said. He added that the US had shared information gathered from the balloon debris with dozens of other countries. China has denied the balloon was being used for spying purposes, and says it was a weather device blown astray. US officials have described the balloon as being about 200 ft (60m) tall, with the payload portion comparable in size to regional airliners and weighing hundreds - or potentially thousands - of pounds. Its presence in US airspace set off a diplomatic crisis and prompted Secretary Blinken to immediately call off a trip to China - the first such high level US-China meeting there in years. It was later shot down by a US fighter jet off the eastern coast. Citing unnamed officials, the Washington Post reported that the US believes the suspected surveillance balloon project was being operated from China's coastal Hainan province and targeted countries including Japan, India, Vietnam, Taiwan and the Philippines.” | BBC | 2023 |
| FBI | “According to its analysis of the documents in this FBI office, 1 percent were devoted to organized crime, mostly gambling; 30 percent were "manuals, routine forms, and similar procedural matter"; 40 percent were devoted to political surveillance and the like, including two cases involving right-wing groups, ten concerning immigrants, and over 200 on left or liberal groups. Another 14 percent of the documents concerned draft resistance and "leaving the military without government permission." The remainder concerned bank robberies, murder, rape, and interstate theft.” | Noam Chomsky Citizens' Commission to Investigate the FBI | |
| Bill Gates | “Eventually what we’ll have to have is certificates of who’s a recovered person, who’s a vaccinated person […] Because you don’t want people moving around the world where you’ll have some countries that won’t have it under control, sadly. You don’t want to completely block off the ability for people to go there and come back and move around. So eventually there will be this digital immunity proof that will help facilitate the global reopening up.” | Bill Gates | 24 March 2020 |
| ID2020 | “Beyond the enormous economic interests that motivate the promoters of the Great Reset, the imposition of the vaccination will be accompanied by the requirement of a health passport and a digital ID, with the consequent contact tracing of the population of the entire world. Those who do not accept these measures will be confined in detention camps or placed under house arrest, and all their assets will be confiscated.” | Carlo Maria Viganò | 25 October 2020 |
| Logic Industries | “ In 2008 Abu Dhabi authorities agreed to pay an Israeli owned company $816mn to install security systems protecting oil and gas installations in the emirate. Through working with two partner companies former Intelligence agent Mati Kochavi has also won contracts to implement the entire emirate-wide Falcon Eye surveillance project that monitors the movements of all those living in Abu Dhabi.” | ||
| Mobile phone | “A mobile phone is a tracking device that also makes calls” | Julian Assange | |
| Holger Münch | “The still high incidence of punishable hate posting shows a need for police action. Our free society must not allow a climate of fear, threat, criminal violence and violence either on the street or on the internet.” | Holger Münch | 21 June 2017 |
| National Security Agency | “Your Data: If You Have Nothing to Hide, You Have Nothing to Fear” | National Security Agency | |
| Platformization | “Platform businesses, such as Amazon, Google and Facebook, have come to dominate their respective markets. They have generated massive network effects by facilitating exchanges with technology. As these platforms get more popular, their user value increases, leading to a virtuous cycle where the entire market coalesces around them. Their success has benefited consumers, with both low prices and access to more data-driven services. But this has also resulted in winner-take-all dynamics, making them powerful monopolies and preventing new entrants from coming in and attracting the market away from the dominant platforms. While users have come to coalesce around these platforms because their needs are being well-served, their powerful network effects risk guaranteeing their winner-take-all position. In their initial days, these platforms rapidly gained user acceptance by providing value to them. Their benevolence is increasingly looking like dominance. While they have enabled interactions and opened up markets, increasing efficiency for customers and vendors alike, they are attracting scrutiny. Data has become currency and they have a monopoly on it.” | Sangeet Paul Choudary | 8 May 2017 |
| Dick Schoof | “Here you come to the metaphor of the frog in the pan. If you slowly make the water in the pan hotter, the frog would stay put. But if you throw the frog into a hot pan, it jumps right out.” | Dick Schoof | 2023 |
| TSA | “El Reg: "Sonic Screwdriver is cleared aimed at molesting seized machines, or during black bag operations, not at interfering with factory-fresh products in transit."
Do it at airports during a customs inspection. Take the computer out of the owner's sight and install whatever you want. Or better still, come up with some sort of bogus excuse to force everyone to put their laptops in checked baggage, and then do it in the baggage handling process. That way the subject wouldn't know they had been targeted. Not that anyone would ever dream of doing something as disruptive as arbitrarily forcing people to check their laptops of course...” | 23 March 2017 | |
| Peter Thiel | “I believe that it is always important to exchange views with people, no matter what their perspectives are. I think we have a lot of problems in our society and we need to be finding ways to talk to people. We need to find ways to talk to people where not everything is completely transparent. Libertarianism is not synonymous with radical transparency. That’s often an argument that Stasi would make in East Germany, when everything had to be monitored by society. And I think you have the best conversations in smaller groups where not everything is being monitored. That’s how you can have very honest conversations and you can think better about the future.” | Peter Thiel | 2016 |
| Russ Tice | “Why would anyone believe a bloody word of what NSA says about their mass domestic surveillance programs? They have lied repeatedly in the past and they are likely lying now. They have been collecting meta data and content, word-for-word, both voice and text, for some time now.” | Russ Tice | 2019 |
| UK | “The UK's communications watchdog Ofcom has overturned its ban on the use of GSM gateways (COMUGs) for overseas phone calls – leaving one of the longest prosecutions in modern English legal history hanging in the balance. The decision comes after a controversial public consultation exercise held earlier this year, in which The Register caught the Home Office's secret spy powers unit trying to anonymously lobby the regulator and keep the ban.” | Gareth Corfield | 10 July 2017 |
| UK/Deep state | “The UK's communications watchdog Ofcom has overturned its ban on the use of GSM gateways (COMUGs) for overseas phone calls – leaving one of the longest prosecutions in modern English legal history hanging in the balance. The decision comes after a controversial public consultation exercise held earlier this year, in which The Register caught the Home Office's secret spy powers unit trying to anonymously lobby the regulator and keep the ban.” | Gareth Corfield | 10 July 2017 |
| Naomi Wolf | “I am not overstating this, I can't say it forcefully enough, this is literally the end of human liberty in the West if this plan [of vaccine passports] unfolds...” | Naomi Wolf | 29 March 2021 |
Related Documents
| Title | Type | Publication date | Author(s) | Description |
|---|---|---|---|---|
| Document:10 Ways We Are Being Tracked Traced and Databased | blog post | 10 July 2010 | 'Activist' | A summary overview of technological developments in the main branches of surveillance technology with examples of their current and developing application. |
| Document:Google and the NSA | article | 24 August 2013 | Julian Assange | |
| Document:Hacker Generations | article | 23 August 2011 | Richard Thieme | On the origins and real meaning of "Hacker"; a term which, in company with "conspiracy-theory", "Holocaust-denial" and many others has been co-opted/invented by Establishments to marginalise research deemed most threatening to the Official Narratives that define "Consensus trance" reality. |
| Document:Hacking on a Scale you can Barely Imagine | article | 6 December 2012 | John Pilger | On the glaring omissions and hypocrisies of the Leveson Inquiry into Press standards, noting especially the vast covert programs of interception and permanent storage of every item of electronic communication on the planet for later data-mining wherever the state might deem it expedient to re-construct the life and movements of targetted individuals. |
| Document:Julian Assange at Moment of Truth | Video transcript | 15 September 2014 | Julian Assange | Speech by Julian Assange to the Moment of Truth event in New Zealand on 15 September 2014 |
| Document:NSA GCHQ and the Death of Gareth Williams | article | 14 November 2011 | Trowbridge Ford | A speculative article connecting the NSA with the death of Gareth Williams |
| Document:The Essential Rules of Tyranny | webpage | 29 July 2011 | Brandon Smith | |
| Document:The demise of global communications security | Wikispooks Page | 21 September 2005 | Wayne Madsen | |
| Document:Unthinking extremism - Radicalising narratives that legitimise surveillance | paper | 26 October 2015 | Ben Harbisher | |
| File:Dissent or Terror FINAL 0.pdf | report | 20 May 2013 | Beau Hoda | Dissent or Terror a report that details how the counter-terrorism apparatus was used to monitor the Occupy Movement nationwide |
| File:Full-Disclosure.pdf | report | 4 December 2013 | The Adversaries | If your UK internet service and equipment provider is BT (and probably any other of the large UK ISP's), then it is a trivial matter for GCHQ and its agencies to route a duplicate of all your traffic to a spook server, access your home computer network, install malware and retrieve any passwords and encryption keys stored on it. You have been warned. |
| File:Operation-shady-rat.pdf | report | 2 August 2011 | Dmitri Alperovitch |
Rating
Although rather wordy and in need of better structure, this page gathers a lot of relevant information in one place and presents insight into this important topic.
References
- ↑ http://www.911truth.org/trump-bush-had-advanced-notice-of-911/
- ↑ http://www.911truth.org/trump-bush-had-advanced-notice-of-911/
- ↑ http://www.theregister.co.uk/2017/03/10/united_nations_special_rapporteur_on_privacy_report/
- ↑ http://www.rt.com/uk/314157-britain-surveillance-dangerous-un/
- ↑ Robert H. Ferrell (ed.) Dear Bess: The Letters from Harry to Bess Truman, 1910-1959 (New York: W. W. Norton, 1983), 550.
- ↑ https://techcrunch.com/2019/07/26/siri-recordings-regularly-sent-to-apple-contractors-for-analysis-claims-whistleblower/
- ↑ https://www.naturalnews.com/2019-01-10-google-caught-secretly-recording-conversations-mobile-device.html
- ↑ https://www.vice.com/en_us/article/43kv4q/microsoft-human-contractors-listened-to-xbox-owners-homes-kinect-cortana
- ↑ http://gizmodo.com/u-s-post-offices-have-installed-hidden-spy-cameras-to-1691112318
- ↑ http://www.motherjones.com/kevin-drum/2013/06/nsa-claims-it-doesnt-track-movements-cell-phone-users
- ↑ http://web.archive.org/web/20150417071618/http://radar.oreilly.com/2011/04/apple-location-tracking.html
- ↑ http://www.defensenews.com/story/defense/international/europe/2014/12/17/italian-reaper-drones-to-be-used-for-crowd-monitoring/20528495/
- ↑ http://www.usatoday.com/story/news/2015/01/19/police-radar-see-through-walls/22007615/
- ↑ Timm, Trevor (2013-02-12). "As Secretive "Stingray" Surveillance Tool Becomes More Pervasive, Questions Over Its Illegality Increase". Electronic Frontier Foundation. Retrieved 2014-06-23.Page Module:Citation/CS1/styles.css must have content model "Sanitized CSS" for TemplateStyles (current model is "Scribunto").
- ↑ http://www.propublica.org/article/judge-orders-nypd-to-release-records-on-x-ray-vans
- ↑ http://21stcenturywire.com/2015/01/29/revealed-the-tsas-new-computerized-facial-and-emotional-recognition-system/
- ↑ http://motherboard.vice.com/read/us-customs-quietly-launches-facial-recognition-experiment-at-dc-airport
- ↑ https://www.laphamsquarterly.org/spies/under-watchful-eyes Lapham's Quarterly